Multiplatform ransomware gains steam - Here's how to protect your business from ransomware attacks
The recent investigation by Kaspersky experts uncovered the activity of RedAlert and Monster – groups that managed to perform attacks on different operating systems without resorting to multiplatform languages.
Kaspersky has discovered new ransomware gangs that have learnt to adapt their malware to different operating systems at the same time, and therefore cause damage to more organizations. Particularly, the team of experts from Kaspersky has uncovered the activity of RedAlert and Monster – groups that managed to perform attacks on different operating systems without resorting to multiplatform languages.
Kaspersky security researchers have been witnessing the prolific use of cross-platform amenities by ransomware groups, aiming to damage as many systems as possible by adapting their malware code to several OS at the time. However, this time the reported ransomware groups deploy malware that is not written in a cross-platform language, but still can target various OS simultaneously.
Kaspersky also commented on the so-called 1-day exploits, which usually refers to an exploit of already patched vulnerability, used to attack on Windows 7-11. Particularly interesting about these exploits is that they support a variety of Windows versions, which usually indicates that the attackers are aiming at commercial organizations.
Kaspersky shares below tips on how consumers and businesses can protect themselves from ransomware attacks .
RedAlert and Monster: multiplatform ransomware gains steam
24 August 2022
In line with the trend for the cross-platform ransomware, Kaspersky has discovered new ransomware gangs that learned to adapt their malware to different operating systems at the same time – and therefore cause damage to more organizations. The recent investigation by Kaspersky experts uncovered the activity of RedAlert and Monster – groups that managed to perform attacks on different operating systems without resorting to multiplatform languages. Additionally, the experts described 1-day exploits that may be executed by ransomware groups in order to achieve their financial ambitions.
During 2022, Kaspersky security researchers have been witnessing the prolific use of cross-platform amenities by the ransomware groups. These days, they’re aiming at damaging as many systems as possible by adapting their malware code to several OS at the time. Kaspersky has already described such groups that used Rust or Golang multiplatform languages – for example, Luna or BlackCat. However, this time the reported ransomware groups deploy malware that is not written in a cross-platform language, but still can target various OS simultaneously.
One group, RedAlert, employs malware written in plain C – as it was detected in Linux sample. However, the malware developed by RedAlert does explicitly support ESXi environments. Moreover, the RedAlert onion website offers a decryptor for download – unfortunately, there’s no extra data available whether it’s written in cross-platform language or not. Another aspect that sets RedAlert apart from other ransomware groups is that they only accept payments in Monero cryptocurrency – making the money harder to trace. Although such an approach might be reasonable from criminals’ point of view, Monero is not accepted in every country and by every exchange, so victims might face a problem with paying off the ransom.
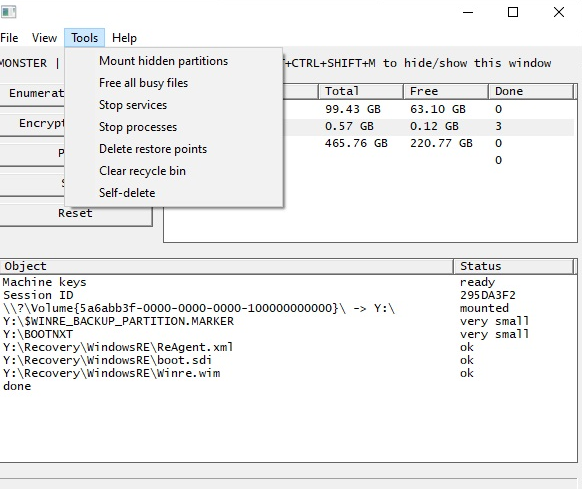
Another ransomware group detected in July 2022 is Monster that applies Delphi, a general-purpose programming language to write their malware that, however, expands on different systems. What makes this group especially peculiar is that it has a graphical user interface (GUI) – a component that has never been implemented by ransomware groups before. Moreover, cybercriminals executed ransomware attacks through the command line in an automated way during an ongoing targeted attack. According to the sample extracted by Kaspersky experts, the Monster ransomware authors included the GUI as an optional command line parameter.
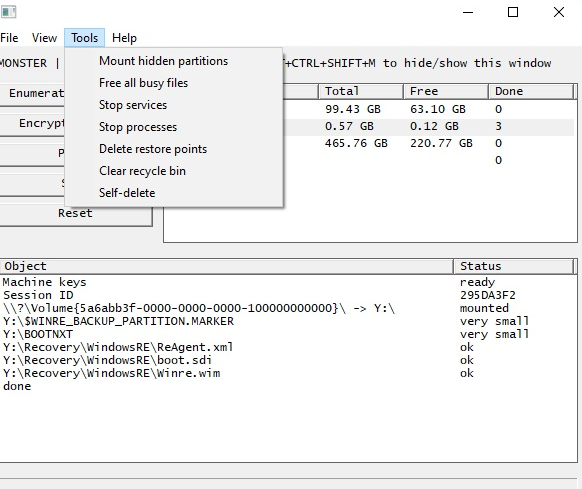
Monster performed attacks on users in Singapore, Indonesia, and Bolivia.
The report issued by Kaspersky also covers so-called 1-day exploits used to attack on Windows 7-11. The 1-day exploit usually refers to an exploit of already patched vulnarability, and always raise a question of patching policy within the affected organization. The given example is about the CVE-2022-24521 vulnerability that allows an attacker to gain system privileges on the infected device. It took attackers two weeks after the vulnerability was disclosed in April 2022, to develop the two exploits. Particularly interesting about these exploits is that they support a variety of Windows versions. This usually indicates that the attackers are aiming at commercial organizations. Also, both exploits share many debug messages. One detected case includes attacks on a retail chain in APAC region – however, there’s no extra data on what the cybercriminals were trying to achieve.
“We’ve got quite used to the ransomware groups deploying malware written in cross-platform language. However, these days cybercriminals learned to adjust their malicious code written in plain programming languages for joint attacks –making security specialists elaborate on ways to detect and prevent the ransomware attempts. Also, we draw attention to the importance of constant reviewing and updating patch policies that are applied by companies,” comments Jornt van der Wiel, a senior security researcher at Kaspersky’s Global Research and Analysis Team.
To learn more about RedAlert and Monster ransomware groups as well as 1-day exploits, please check the full report on Securelist.
To protect yourself and your business from ransomware attacks, consider following the rules proposed by Kaspersky:
- Do not expose remote desktop services (such as RDP) to public networks unless absolutely necessary and always use strong passwords for them.
- Promptly install available patches for commercial VPN solutions providing access for remote employees and acting as gateways in your network.
- Always keep software updated on all the devices you use to prevent ransomware from exploiting vulnerabilities
- Focus your defense strategy on detecting lateral movements and data exfiltration to the Internet. Pay special attention to the outgoing traffic to detect cybercriminals' connections.
- Back up data regularly. Make sure you can quickly access it in an emergency when needed.
- Use solutions like Kaspersky Endpoint Detection and Response Expert and Kaspersky Managed Detection and Response service which help to identify and stop the attack on early stages, before attackers reach their final goals.
- To protect the corporate environment, educate your employees. Dedicated training courses can help, such as the ones provided in the Kaspersky Automated Security Awareness Platform.
- Use a reliable endpoint security solution, such as Kaspersky Endpoint Security for Business that is powered by exploit prevention, behavior detection and a remediation engine that is able to roll back malicious actions. KESB also has self-defense mechanisms which can prevent its removal by cybercriminals.
- Use the latest Threat Intelligence information to stay aware of actual TTPs used by threat actors. The Kaspersky Threat Intelligence Portal is a single point of access for Kaspersky’s TI, providing cyberattack data and insights gathered by our team for 25 years. To help businesses enable effective defenses in these turbulent times, Kaspersky has announced access to independent, continuously updated and globally sourced information on ongoing cyberattacks and threats, at no charge. Request access to this offer here.